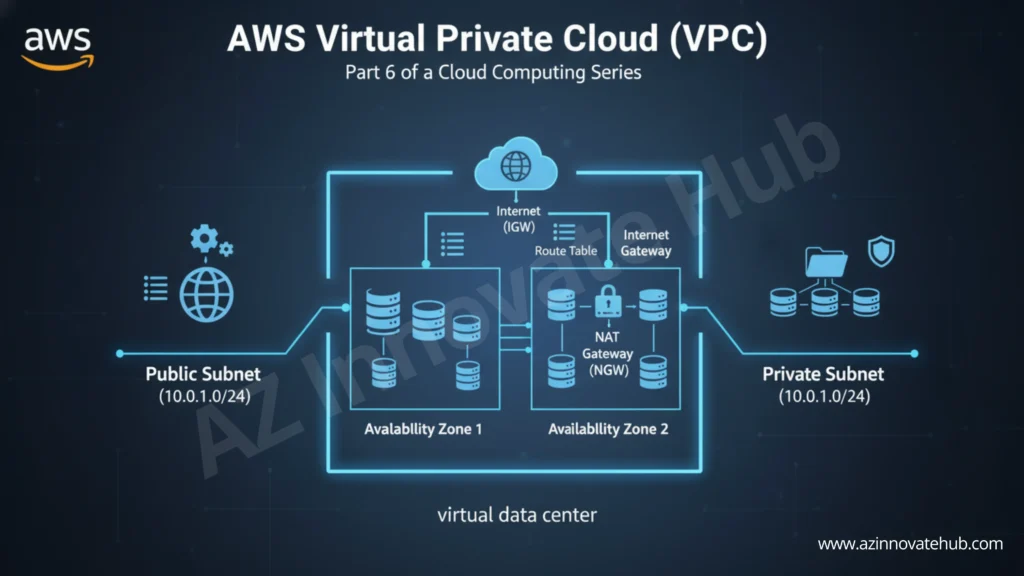
Understanding cloud networking is fundamental to designing any secure solution. The foundation of networking in AWS is the AWS VPC, or Virtual Private Cloud.
An AWS VPC allows you to launch AWS resources into a logically isolated virtual network that you define. It gives you a part of the AWS cloud that only your resources can use. It closely resembles a traditional network you would operate in your own on-premises data center. This gives you full control over your cloud network, including security, IP addresses, and subnets.
This virtual network exists within the AWS global infrastructure, which is built around Regions and Availability Zones (AZs).
- Region: A separate geographical location (e.g., US East 1 for North Virginia) where infrastructure is deployed. Regions are independent of each other.
- Availability Zone (AZ): Each region consists of multiple (at least three) AZs. An AZ is one or more discrete data centers with redundant power and networking. AZs are physically separated (e.g., by 50-60 km) to isolate failures like fires or floods. An AWS VPC spans all the AZs in a Region.
IP Addressing and CIDR
When you create an AWS VPS, you must specify a range of IPv4 addresses for it to use. This is done using Classless Inter-Domain Routing (CIDR) notation. The CIDR block defines the entire size of the network.
- A /16 subnet mask (e.g., 172.31.0.0/16) provides up to 65,536 private IP addresses.
- A /24 subnet mask (e.g., 192.168.1.0/24) provides 256 IP addresses.
Subnets: Public vs. Private
You must divide your AWS VPC into smaller network segments called subnets.
- AZ Confinement: A subnet is required to launch resources and is confined to a single Availability Zone.
- Public Subnets: These subnets host resources that need direct internet access, such as a web server.
- Private Subnets: These subnets hosts sensitive resources, like databases, that should not be directly exposed to the internet.
- IP Reservations: In every subnet AWS creates, the first four and the last IP address are reserved for networking purposes (e.g., network address, VPC router, DNS server).
AWS VPC Tenancy
Tenancy refers to the hardware isolation of your instances within the VPC.
- Default Tenancy: This is the most common choice. Your virtual servers may share the same physical hardware with other customers. This resource sharing is what makes the cloud cost-effective.
- Dedicated Tenancy: This option ensures your instances run on hardware dedicated solely to you. It is used for strict compliance or security requirements.
VPC Connectivity Components
To enable communication, your AWS VPC requires several key components:
- Internet Gateway (IGW): This component allows communication between your VPC and the public internet. You can only attach one IGW per VPC.
- Router Tables (RT): An IGW alone is not enough. Route Tables contain rules that control network traffic. To make a subnet “public,” you must add a rule to its associated Route Table that directs all internet-bound traffic (destination 0.0.0.0/0) to the Internet Gateway.
- NAT Gateway (NGW): Private servers, like databases, sometimes need outbound internet access to download software patches or updates. A NAT Gateway provides this outbound-only access for resources in private subnets. The NAT Gateway must be placed in a public subnet. The private subnet’s Route Table is then configured to route internet traffic (0.0.0.0/0) through the NGW. This prevents external entities from initiating connections to the private resources.
Conclusion: Your Private Corner of the Cloud
You’ve successfully built the blueprint for a secure and isolated cloud network. The AWS VPC (Virtual Private Cloud) is the foundation for all your resources. You now know how to define its IP address space (CIDR), create Public and Private Subnets across different Availability Zones, and control traffic flow using Route Tables.
You’ve learned how an Internet Gateway (IGW) gives public resources internet access and how a NAT Gateway (NGW) allows private resources to get updates securely.
But a network is only secure if you control what comes in and out. In the next article, we’ll cover the “virtual firewalls” of the cloud: Security Groups, NACLs, and the master control service, AWS IAM.